
There are many challenges to monitoring a pipeline - not to mention implementing some sort of leak detection on it. For some pipelines, one of the challenges is simply getting data! Remote locations, access to power and comms are just some of the hurdles that get in the way of operators viewing operational data. We have run into this challenge with some of our customers and partners in particular as we seek to obtain data from rural pipelines or remote test sites.
![]() Fortunately, there is technology available now that can help overcome these obstacles - and it is becoming more accessible. Modern IoT (internet of things) developments have produced several options for collecting site data and either processing it locally or transmitting it to the cloud for use elsewhere. IoT gateways - or "Edge devices" - can provide a lightweight means for data collection and transmittal. We have worked with third party suppliers to offer this technology to customers when flow rate or pressure data is needed but not readily available through existing SCADA set-up.
Fortunately, there is technology available now that can help overcome these obstacles - and it is becoming more accessible. Modern IoT (internet of things) developments have produced several options for collecting site data and either processing it locally or transmitting it to the cloud for use elsewhere. IoT gateways - or "Edge devices" - can provide a lightweight means for data collection and transmittal. We have worked with third party suppliers to offer this technology to customers when flow rate or pressure data is needed but not readily available through existing SCADA set-up.
We've also used it extensively for our own purposes to collect data from a withdrawal test skid that we use frequently for validation tests.
When conducting our fluid withdrawal tests (FWTs), the test skid is often in remote locations where there is no station - let alone power or comms. And yet, it is very useful for us to have that real-time access to the 'truth' data from the skid to know when the withdrawal starts, what the 'leak' rate is, etc. Not only is this data used in real time to monitor the test, but we use it immediately after to compare the leak metrics calculated in our software (estimated leak start, estimated leak size, estimated leak volume, etc.) to the 'truth' data from the skid and verify accuracy.

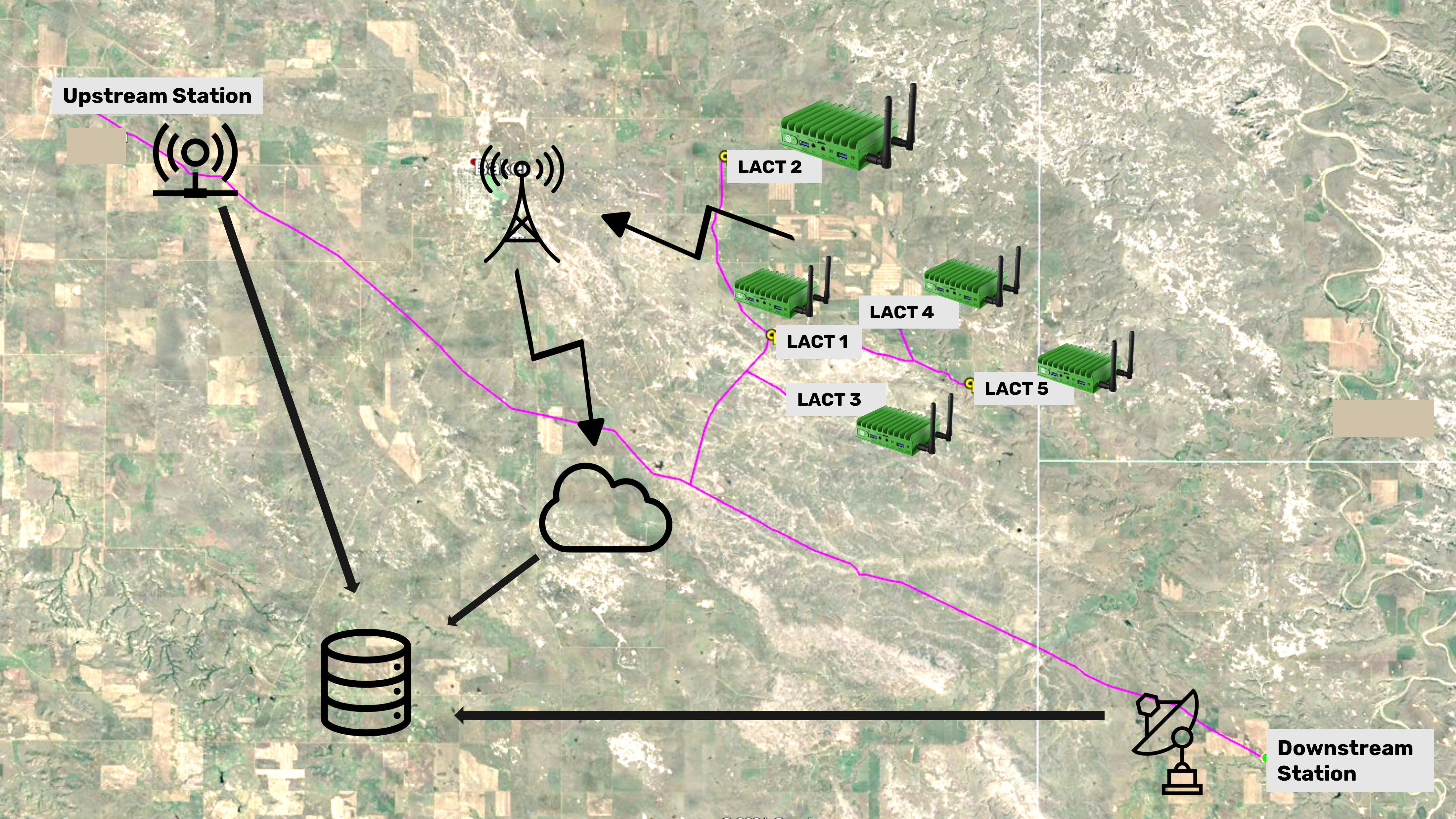
For pipeline operators, this technology can be very helpful in filling in the gaps - like in this example below where meter data may not be available from LACTs on gathering line injections. Data can be collected using an edge device, transmitted by cell to the cloud, and then integrated with primary station data to enable composite leak detection for the full segment.

Is using an edge device secure?
Fortunately, there are also many modern technology features available to make sure data collected using an edge device is secure and adheres to security standards. If you would like to know more, Nick, our Director of Cybersecurity and IT would love to have that discussion with you!


Comments
Add Comment